Aws Upload Files to Encrypted S3 Bucket
In that location are times when nosotros need to ensure that if somehow, in any case, our information is being hacked then information technology will even so become unusable for the hacker, every bit in social club to access the data, ane must accept to decrypt it start. And so, today we are going to larn about "encrypt objects during upload to S3 saucepan".
This means that during the upload of a particular object to an S3 bucket, the object is going to be "auto encrypted" using the specified method.
We have following encryption methods available on AWS S3 (as of May 2019):
- Customer Side Encryption
- AES 256 – SSE S3 (Server Side Encryption)
- SSE-C (Server Side Encryption)
- SSE-KMS (Server Side Encryption)
- Encryption in Transit
Note: Today we are going to acquire about "Server Side AES 256 – SSE S3 Encryption".
To learn more than nearly S3 Encryption, follow -> Encryption on objects in an S3 bucket
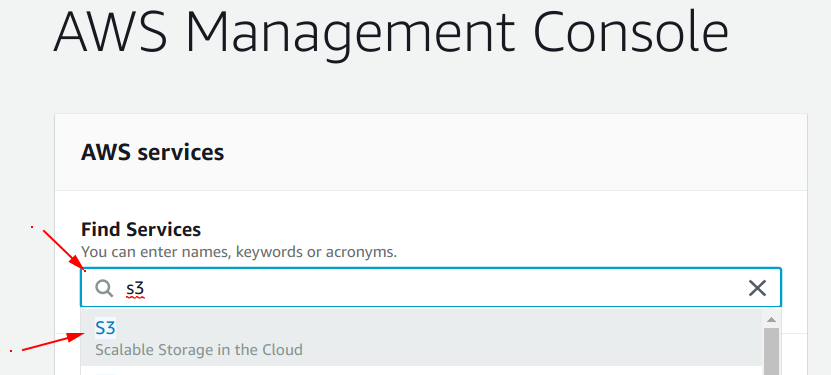
Step 1: Go to S3 dashboard
Search for the "S3 service" under the "Observe Services" section of your "AWS dashboard" and select it.
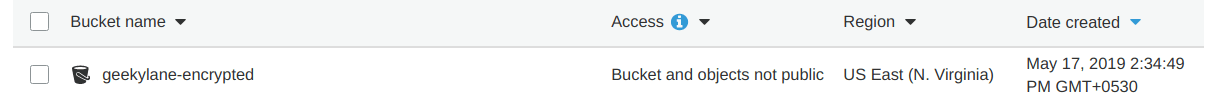
Pace 2: Create a new S3 bucket
In our case, we have created a bucket with a name "geekylane-encrypted", shown in the motion-picture show below.
If you are new to Amazon S3 and do not know about S3 bucket creation, follow -> How to create an S3 bucket on AWS
Now, in order to specify the "auto encryption" of objects during the upload, we take to set some rules for our bucket.
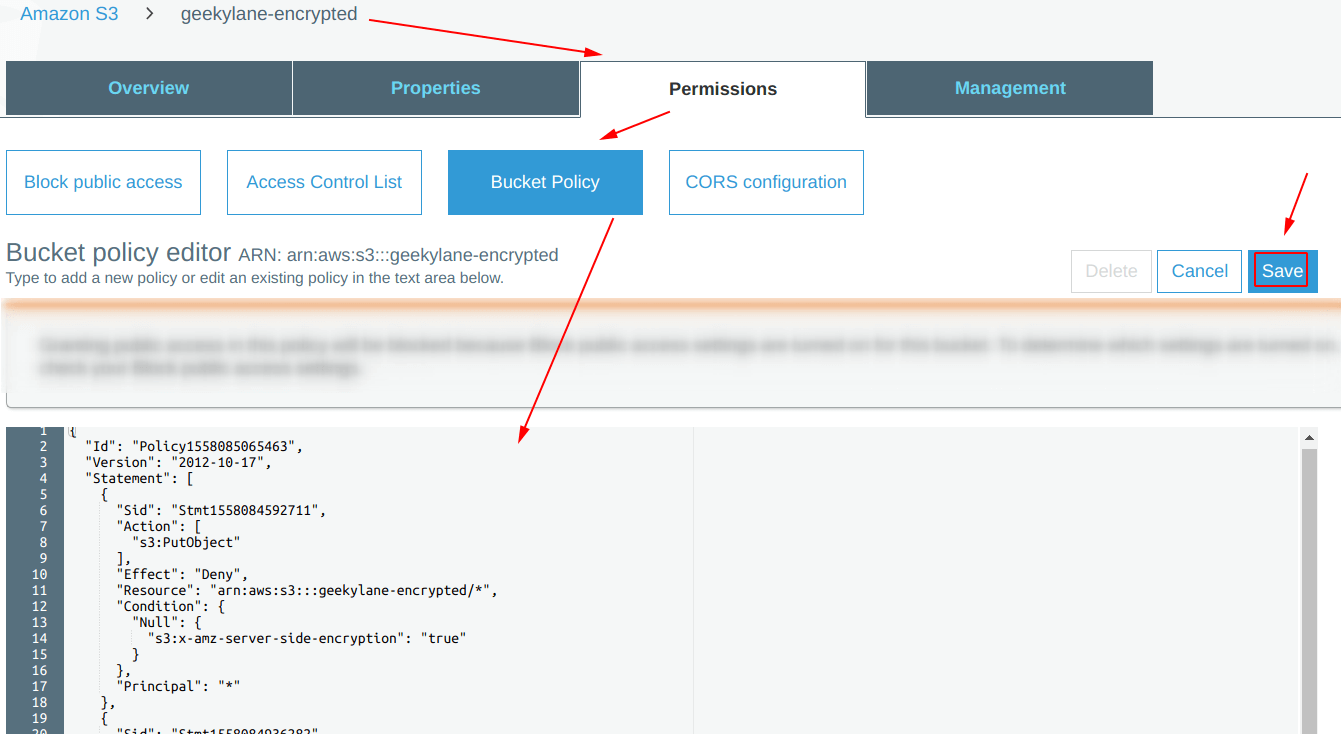
Note: We are going to employ the "bucket policy" method to specify rules on our S3 bucket.
Step 3: Copy the ARN of S3 saucepan
Under the "Permissions" tab, we have post-obit option available:
- Block Public Access
- Admission Control List
- Bucket Policy
- CORS Configuration
Nosotros are going to employ "Bucket Policy".
So, in society to re-create the "ARN" or S3 bucket follow as shown below. In our case, our S3 bucket'southward "ARN = arn:aws:s3:::geekylane-encrypted".
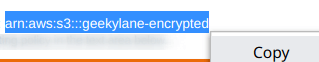
Pace 4: Generate bucket policy using "Policy Generator"
From the picture below, select the "policy generator" from the beneath of this screen.
Question: Why we are using "policy generator"?
Respond: It will help us in creating the specific and complex type of bucket policies with one click.
Later clicking on that, you will be seeing something like shown below.
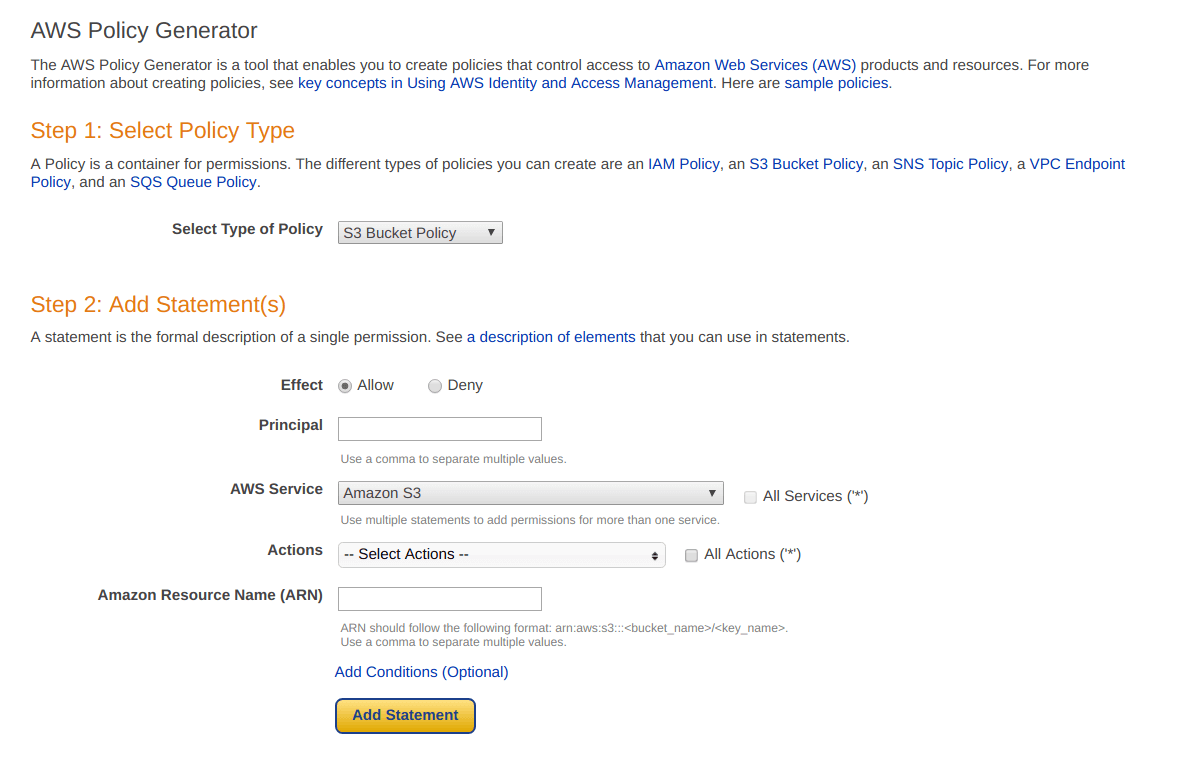
We have created the following two statements for our S3 bucket.
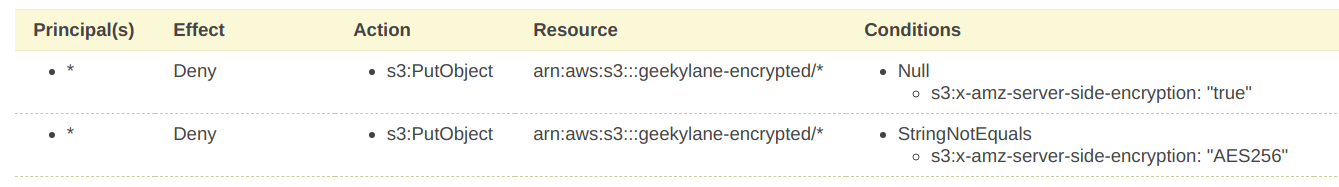
Explanation of Statements mentioned above:
- If the object being uploaded is having the "s3:10-amz-server-side-encryption == NULL", deny its upload, as a result, nosotros are forcing it to add the header.
- If the "s3:x-amz-server-side-encryption != AES256", deny its upload, as a result, the object being upload must have the header value equals to this.
After specifying the two statements, we now accept to "generate policy", as shown below.
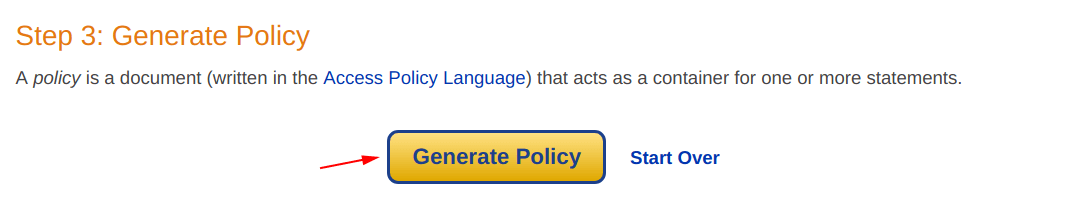
Finally, our bucket policy has been generated successfully. Copy the "JSON Document" in order to use it nether the bucket policy permissions of the "geekylane-encrypted" bucket.
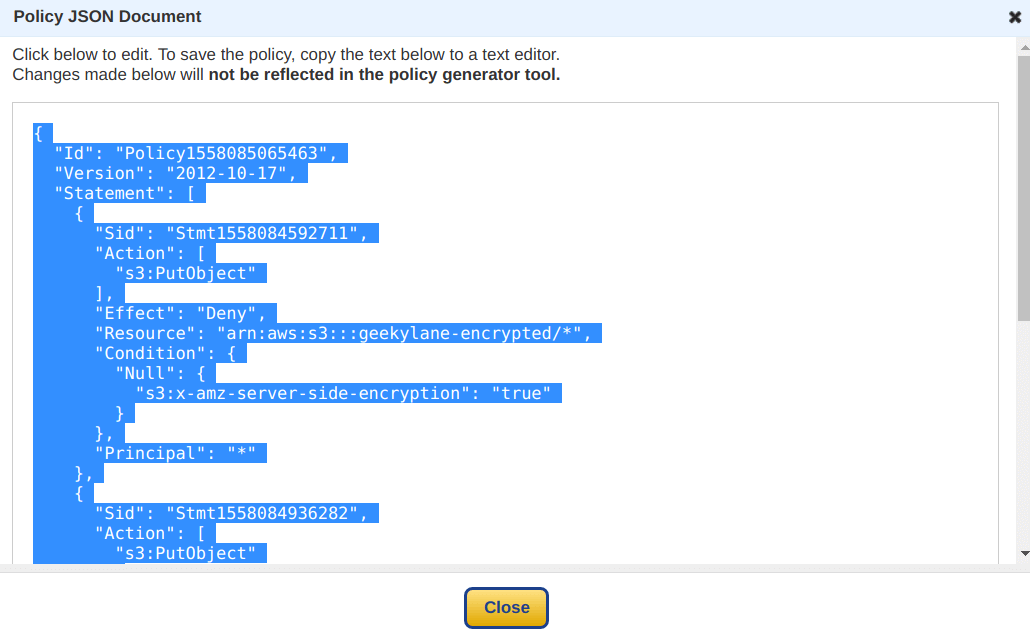
Stride 5: Specify the bucket policy
Paste the policy copied in the "Stride four" as shown below, and hit "Salve".
Step vi: Upload File – Direct Upload
It is time to check whether our bucket policies are working every bit intended or not.
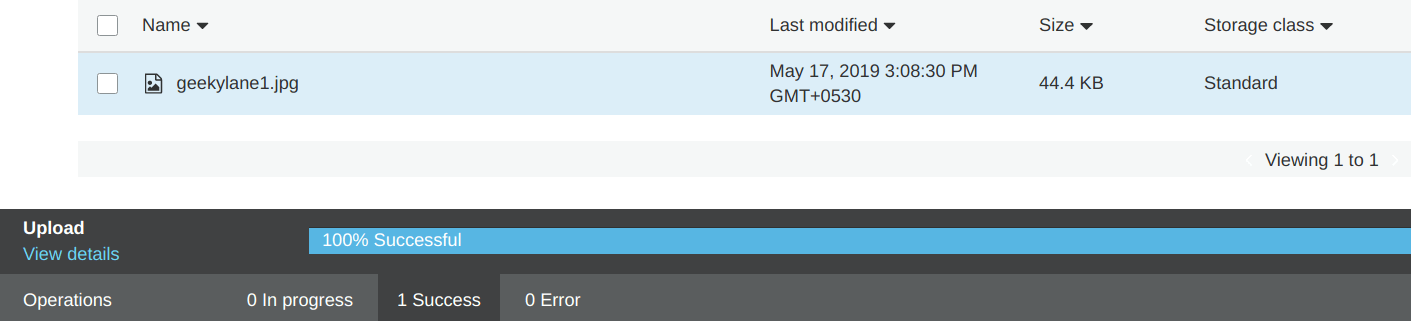
Upload some files to the S3 bucket, in our case, we have tried uploading a file with the proper noun "geekylane1.jpg".
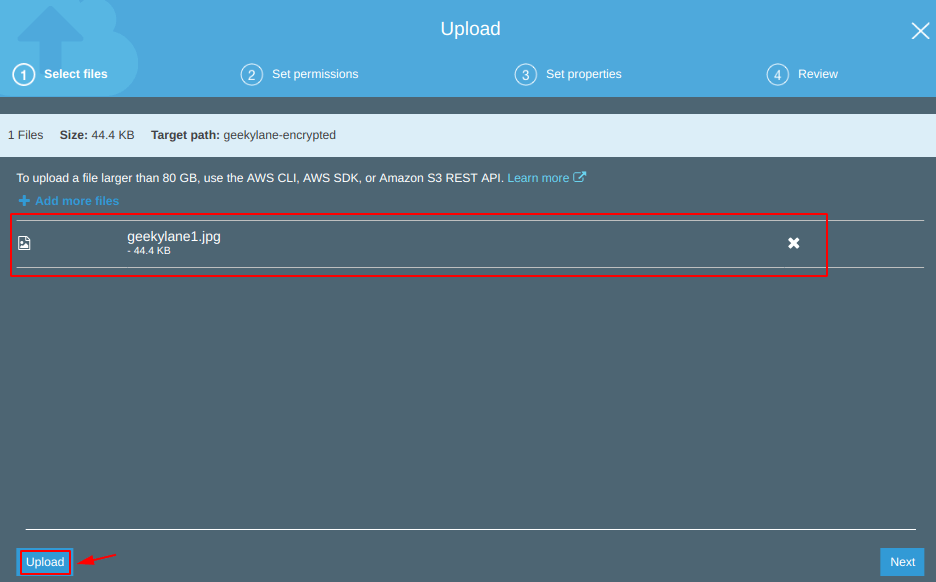
Expect! the "geekylane1.jpg" file upload has been failed, information technology is showing a "100% Failed" error, as shown below.
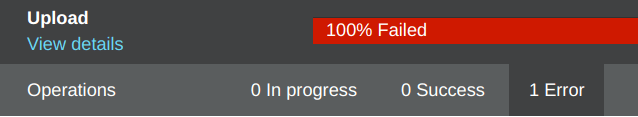
Question: What is happening?
Answer: The thing is that by default the S3 does not upload files using any encryption methods, we accept to manually specify it. Our first try for "geekylane1.jpg" has been failed considering of this reason.
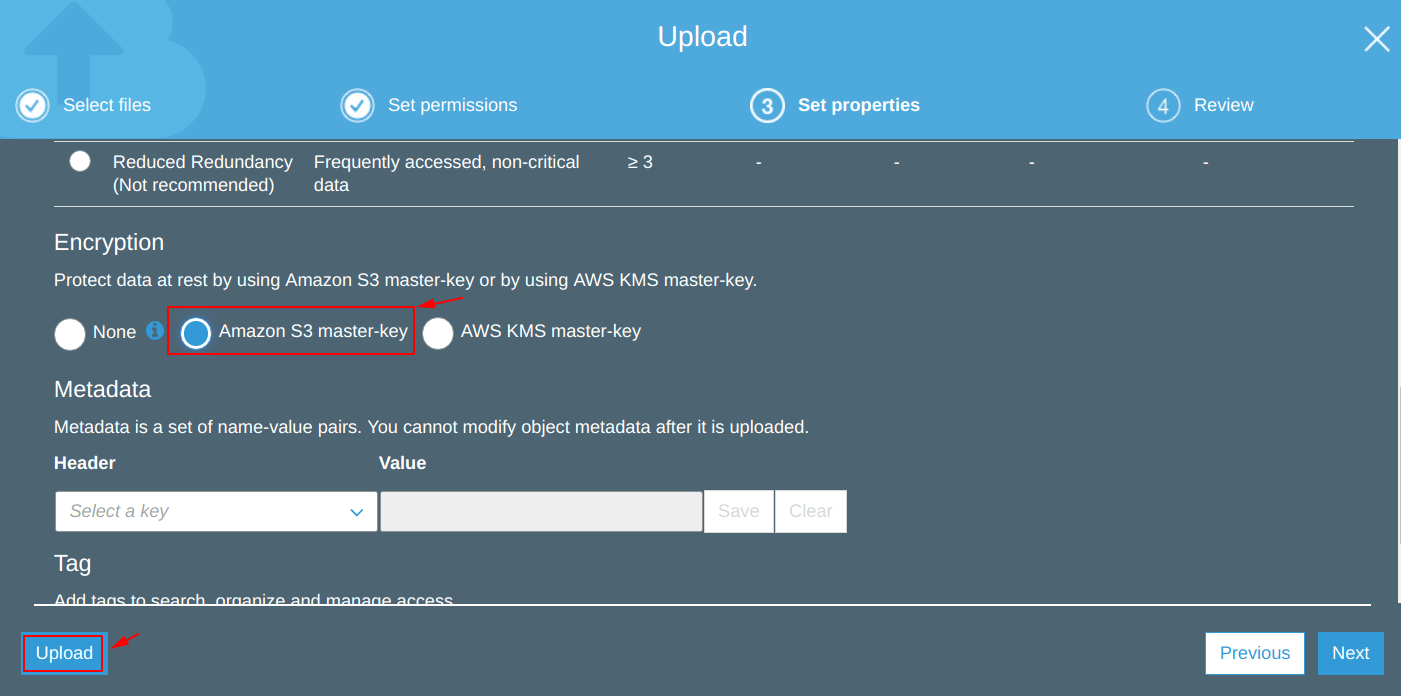
Step 7: Upload File – Using S3 chief-primal Encryption
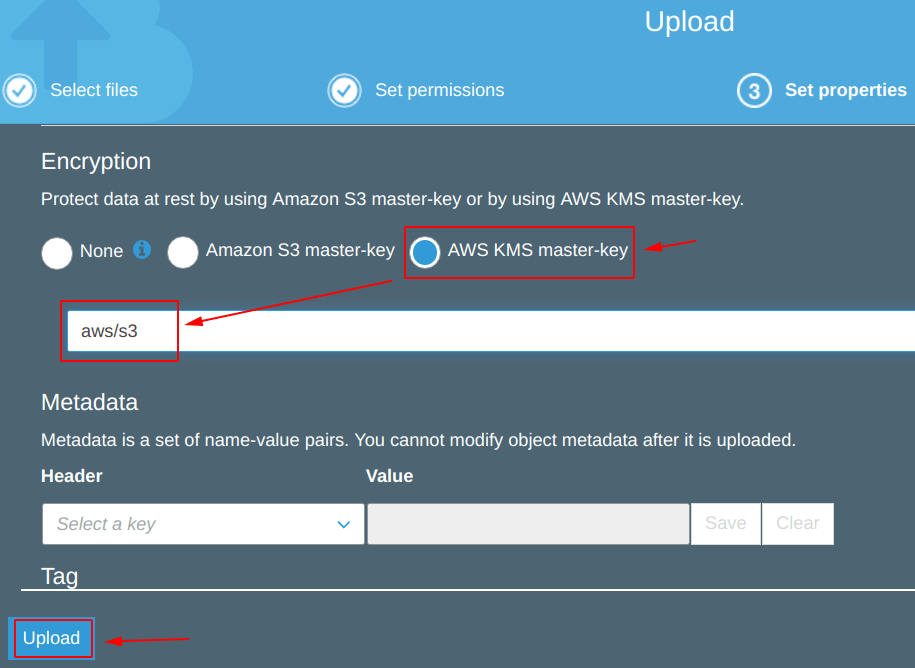
Now, we are specifying the type of encryption which needs to exist done on the objects beingness uploaded in the "geekylane-encrypted" saucepan.
Nosotros are using "Amazon S3 principal-key" encryption which is actually "Server Side AES 256 – SSE S3 Encryption", and this is the type nosotros have specified in our S3 bucket policy.
And then, from the paradigm below we can ostend that the file "geekylane1.jpg" has been uploaded successfully using the "Server Side AES 256 – SSE S3 Encryption".
Pace 8: Upload File – Using AWS KMS primary-key
Now, we are trying to upload and encrypt the object using "AWS KMS principal-key" encryption.
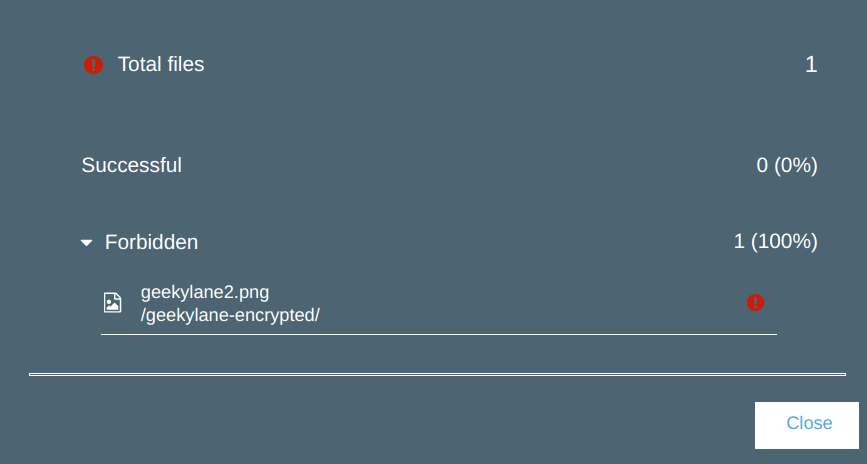
From the photo beneath, we tin can see that it has failed to upload.
Question: What is happening hither?
Answer: It has failed to upload considering we accept not specified this type of encryption inside our bucket policy, which nosotros have created in "Pace four".
Conclusion for "Encrypt Objects During Upload to S3 Bucket"
- Bucket policies are powerful
- Considering nosotros have simply specified explicitly about the "Server Side AES 256 – SSE S3 Encryption" in our saucepan policy in "Step iv", that is why the object/file fails to upload in "Step 6" & "Step 8" but not in "Step 7".
More on S3:
- Enable the cantankerous region replication on S3?
- How to fix lifecycle rule on an S3 saucepan?
- Enable version control on an S3 saucepan?
Related tags :
Source: https://geekylane.com/encrypt-objects-during-upload-to-s3-bucket/
0 Response to "Aws Upload Files to Encrypted S3 Bucket"
Post a Comment